Smart grid technologies that will change the energy sector
in cooperation with CESI - by Davide Piccagli
The evolution of grid assets toward more flexible and smarter operation criteria is key to favor an accelerated roadmap towards a fully decarbonized power system. This process relies on the concept of the “smart grid”. The future of the smart grid will leverage on four main pillars:
- advanced connectivity
- mobile access to the operational technology (OT) systems
- big data
- cybersecurity
Advanced connectivity
One of the main enablers in such a scenario will certainly be the deployment of advanced connectivity. Its availability will be crucial for widespread mobile access to the OT systems. Such a topic represents one of the main changes in daily workforce operations. In the near future, 5G will be a technology of paramount importance to support the deployment of mobile access to the OT systems and the widespread use of all the applications that leverage on advanced connectivity.
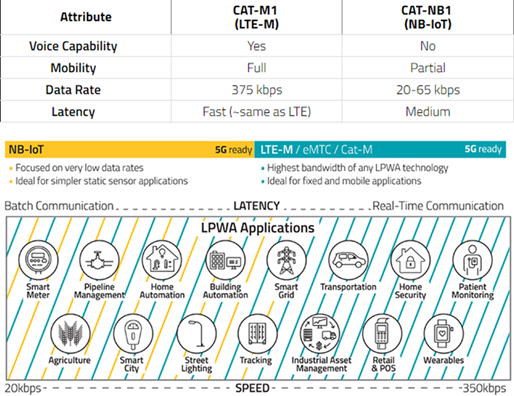
5G technology offers different performances based on the applications. The latency and communication speed are two main performance indicators as shown in Figure 1.
The advanced connectivity relying on 5G technology is the basic smart grid pillar that has implications on mobile access to the OT systems, on the huge data set management (big data), and (cyber-)security (cyber).
Mobile access to OT systems
The advent of smartphones and tablets has given a big push to the possibility of using OT on remote device applications. In the past, power systems data and control systems were strictly relegated to centralized systems. In the last ten years, in fact, the update and the upgrade of OT applications have transformed a large part of legacy platforms in tools based on modern frameworks, which exploit connectivity and remote access.
The features and functionalities of such OT applications have also changed their look, passing from the desktop design to the touchscreen one, which typically is more immediate and user-friendly. This process has involved OT systems in different industrial sectors, comprising the electric one where it has brought about changes in daily tasks both for workers and engineers. The use of mobile devices may include, but is not limited to, the following fields of application:
- field measurement
- asset management
- operation management
- predictive maintenance
- real-time monitoring and control of the network/plants
An interesting example to show the impact of these changes and the advantages provided by mobile apps are systems for the management of survey campaigns of field measurements produced by mobile terminals. Such systems have been created with the aim of facilitating the operations performed on the field for the measurement of manual instrumentation. These systems usually consist of an application to be installed on smartphones/tablets and a software platform to be used on the central system. Such a platform allows the transfer of configurations to the mobile devices’ memory and the reception of data acquired by such devices for subsequent storage in the historical database of measurements.
In some cases, these applications are empowered by augmented reality tools and advanced functions which are particularly useful for the electric utility workforce to perform on-field maintenance. In such cases, these applications allow technicians, through mobile devices, to leverage the collected data for analysis purposes and quickly find an effective solution to the problem on-site.
Furthermore, these applications in some cases can benefit also from the connection with the centralized systems for predictive maintenance. Such systems can be fed by data collected from the technicians in plants and stations and then used for scheduling and optimizing maintenance interventions (in recent years exploiting also Artificial Intelligence).
Big data management
Intelligent Electronic Device (IED), sensors and the “Internet of Things” IOT will generate a large amount of data to be managed, so adequate storage systems, telecommunication networks and proper architecture must be used to deal with the so-called “data lake”.
The data lake shall be seen as a primary resource for the update of operating procedures and processes.
The introduction of algorithms and analyses able to extract and correlate information, using also machine learning and analytics techniques, implies the implementation of a related data process. Such a process can have as outputs both new monitoring outcomes (warnings and alarms), that can be used by the operators to make decisions, and triggers for automated actions. Such operator decisions and automated actions must be previously defined in operating procedures.
Cybersecurity
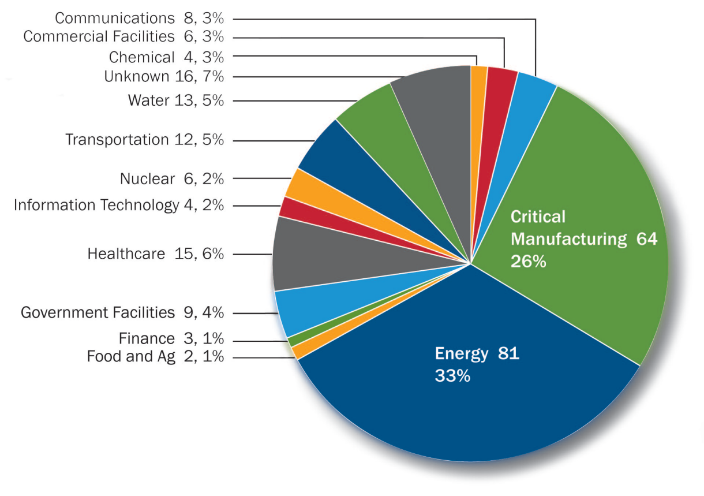
Cybersecurity is already a real risk. In the US, the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) received and responded to more than 245 incidents in one year. Energy is the sector more prone to cyberattacks.
The data stolen from energy companies seems to be aimed at mapping critical infrastructures and collecting detailed information about them, rather than causing blackouts. If not adequately detected and contained, the cyber threats can go on for a long time (advanced persistent threats) and can impact networks, plants, monitoring systems and information relating to employees. It is worth highlighting that only a part of these have been properly investigated in recent years. The stolen data makes it possible to reconstruct the operating criteria of companies, exposing them to ever greater risks. Luckily, so far most of the time the attacks are aimed at obtaining information rather than causing blackouts on the network. However, this information can be used in the future for targeted attacks.
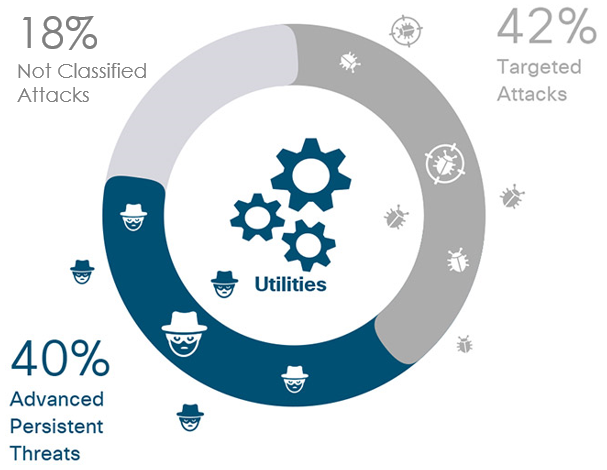
Thus, to effectively implement barriers against cyberattacks, the environment where the data flows, notably based on 5G technology, shall be carefully designed and monitored. High requirements in terms of guaranteed bandwidth and cybersecurity level must be requested to the network providers to satisfy all the actors’ needs. So, not only the large amount of data that will be acquired, but also the interaction among different actors, systems, and security levels must be considered. To build a “trust chain” that covers all the domains is of crucial importance.
In such a highly connected environment, 5G introduces new technologies and devices that can create new risks, strictly connected to the new technology (e.g. enlarged exposure surface, number of connected devices and shared network resources). In addition, it increases the likelihood of existing threats because new access points (IED, IOT devices, etc.) can be exploited to enter the OT systems.
The “security by design” principle states that if security is not designed from the beginning surely there will be problems. This principle is essential, and for OT systems security by design implies resilience by design: The OT systems must be able to respond and recover the full availability in a short time. Since a zero risk condition does not exist, an efficient resilience scheme should be planned from the very beginning to protect the OT systems. Moreover, cybersecurity implementation and updates are needed since OT systems are affected by a “legacy” problem (the large majority of industrial equipment are based on legacy infrastructure).
In summary, to best exploit all the opportunities offered by 5G technology, it is crucial to face its introduction with a holistic approach. This implies involving all the levels of the utilities, to create synergy among smart grid actors, to harmonize IT and OT requirements and needs, and, last but not least, to consider cybersecurity as the key factor in deploying efficient and resilient OT systems.
Smart grids for the energy transition – in cooperation with CESI
